Cybersecurity and data-compliance due diligence has evolved from a routine risk-mitigation exercise into a decisive factor that can determine the success or failure of mergers and acquisitions involving Chinese targets. This article examines the legal framework underpinning that shift, identifies five core areas of diligence that buyers must scrutinise, analyses recent enforcement actions and landmark cases, and proposes contractual mechanisms to allocate compliance risks in transaction documents.
Introduction
Once a peripheral concern, cybersecurity and data compliance is now a central value driver – and a potential deal-breaker – in M&A transactions involving Chinese companies. This transformation is driven by a rapidly evolving regulatory landscape, which between 2016 and 2025, involved the promulgation of three foundational data-protection laws – one of which was substantially revised, the creation of a framework of implementation regulations and national standards, and the very gradual escalation of enforcement actions across multiple sectors.
Recent notable developments in 2026 include:
- In January, the newly amended Cybersecurity Law (2025 CSL) entered into force.
- Also in January, the Shanghai Cyberspace Administration published model enforcement cases spanning network data security, cross-border data transfers and personal information protection (2025 Shanghai Cases; Shanghai CAC, Model Cases on Network Data Security Protection, 16 January 2026).
- In April, the National Development and Reform Commission (NDRC) used its foreign investment security review authority for the first time to block a major cross-border AI acquisition on data-security grounds – the Meta-Manus deal (2026 Manus Review; NDRC Foreign Investment Safety Review Office, Decision to Prohibit Foreign Capital’s Acquisition of the Manus Project, 27 April 2026).
For buyers, sellers and their advisers, the message should now be clear: data compliance can affect corporate valuations, and, in some cases, whether a deal can proceed at all.
The Regulatory Architecture: A Three-Pillar Framework
China’s data-protection system rests on three pillars, each imposing distinct but overlapping obligations.
The Cybersecurity Law
The Cybersecurity Law was first enacted in 2016 (2016 CSL) and was amended by the NPC Standing Committee on 28 October 2025, with the amendments taking effect on 1 January 2026 (2025 CSL). The 2025 CSL mandates basic cybersecurity obligations for network operators and requires the implementation of the Multi-Level Protection Scheme (MLPS), a classification system for information systems (Articles 23 and 33).
The amendments in the 2025 CSL recalibrate penalty thresholds to align with the Data Security Law (2021 DSL) and the Personal Information Protection Law (2021 PIPL), embed support for artificial intelligence, and introduce extraterritorial provisions allowing China to pursue overseas actors whose data-related activities damage China’s national security or public interest (2025 CSL, Article 77).
Under the revised 2025 CSL, penalties for serious violations are tiered: where violations lead to very serious consequences – such as the loss of primary functions of critical information infrastructure – authorities may impose fines of up to RMB 10 million on organisations and fines of up to RMB 1 million on the persons responsible (Article 61).
The Data Security Law
The 2021 DSL took effect in September 2021. It establishes a classified and graded data-protection system. Article 21 of the 2021 DSL requires the State to establish such a system “in accordance with the degree of importance of data to economic and social development” and the damage that would result from tampering, destruction, leakage or illegal use, and to issue catalogues for important data. Data that bears on national security, the lifelines of the national economy, important aspects of people’s livelihood and major public interests is defined as “core data” and is subject to a stricter management system (2021 DSL, Article 21). As such, the 2021 DSL creates three data tiers: general data, important data and core data – with compliance obligations increasing at each level.
The Personal Information Protection Law
The 2021 PIPL took effect in November 2021. For M&A transactions, two provisions are especially important for governing the data transfers that will occur during due diligence.
Article 22 of the 2021 PIPL governs the transfer of personal information in the event of a merger, division, dissolution, or declaration of bankruptcy. This provision applies only to transfers resulting from those specific circumstances and does not cover transfers that occur prior to such events (e.g., during due diligence). When Article 22 does apply, the affected individual must be informed of the recipient’s name and contact information, and the recipient must continue to fulfil the obligations of the original personal information processor.
In contrast, Article 23 of the 2021 PIPL addresses the transfer of personal information to any third party outside the scope of Article 22 and requires separate consent. For the purposes of this article, it is enough to note that obtaining separate consent is significantly more onerous than obtaining ordinary consent.
Since due diligence typically takes place before a merger and may ultimately lead to the merger being abandoned, it is difficult to justify such data sharing as being “due to a merger.” Consequently, third-party transfers under Article 23—including those carried out for due diligence purposes—require individuals’ separate consent.
In the context of the 2021 PIPL, the distinction between Articles 22 and 23 is critical because separate consent is a uniquely demanding requirement, and it applies to many pre-merger data-sharing arrangements, including due diligence.
The Network Data Security Management Regulations 2024
The Regulations on Network Data Security Management (2024 Network Data Regs; State Council Order No. 790, effective 1 January 2025) provide the detailed implementing rules for the three laws discussed above. The 2024 Network Data Regs shift the regulatory logic from passive response to proactive control. They require data processors to establish management systems covering the entire data processing workflow, conduct regular security assessments, and maintain records of processing activities.
Cybersecurity Review for Overseas Listings
For network platform operators controlling personal information of more than one million users and proposing to apply for an overseas listing, the Revised Measures on Cybersecurity Review 2021 (2021 Cybersecurity Measures; effective 15 February 2022) mandate a cybersecurity review application (Article 7). This requirement is directly relevant to private equity exits and IPO-ready targets. The threshold of one million users captures a broad range of tech companies.
Five Core Areas of Due Diligence
Drawing on the regulatory framework outlined above, a thorough cybersecurity due-diligence exercise in a typical China M&A transaction must address five distinct areas.
Data Classification and Grading
The due-diligence team must first determine whether the target processes only general data or whether it handles important data or core data. This is not an academic question, and requires a careful analysis based on the actual data processing activities of the target. In some industries, such as civil aviation and finance, regulators have issued granular requirements of what they consider to be important data and how classification should be conducted.
Important data cannot be transferred abroad without a security assessment conducted by the Cyberspace Administration of China (CAC) under Article 4 of the Outbound Data Transfer Security Assessment Measures 2022 (2022 Security Assessment Measures).
A buyer inheriting a target that has failed to classify its data may itself face regulatory action for non-compliance with the 2021 DSL’s mandatory classification obligations. Core data is subject to even stricter controls.
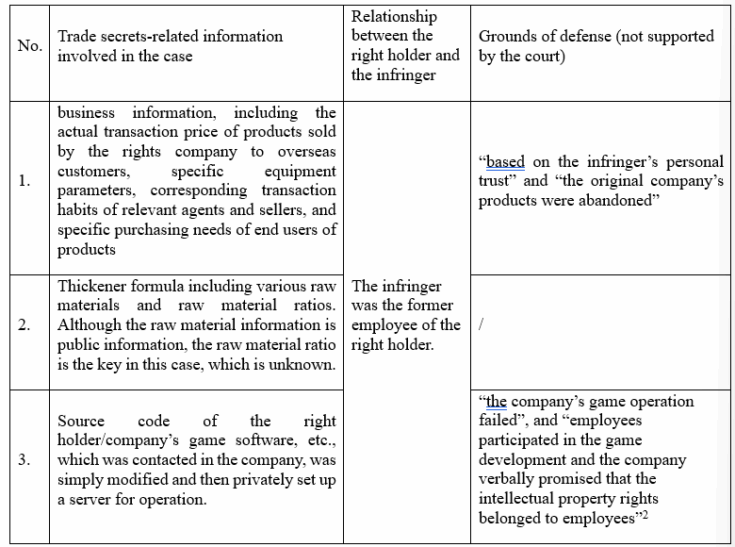
Data Asset Legitimacy and Processing Records
The target’s data assets have value only if they were lawfully obtained. Unlawfully obtained data is a liability subject to potential attack under several laws, including the Copyright Law, Anti-unfair Competition Law, the 2021 PIPL, the 2021 DSL, the Interim Measures for the Management of Gen AI Services, the Criminal Law, and others.
In relation to personal information, due diligence must verify: whether personal information collection was based on proper informed consent or another lawful basis under Article 13 of the 2021 PIPL; whether the target maintains accurate processing records (2021 PIPL, Article 56; 2024 Network Data Regs, Article 12); and whether Personal Information Protection Impact Assessments (PIPIAs) have been conducted for high-risk processing activities (2021 PIPL, Articles 55 and 56).
A target that has no records of a lawful basis is presumed to be processing unlawfully; a target without accurate processing records or data inventories likely cannot coordinate its compliance efforts (because you cannot protect things that are unknown); a target that never conducted a PIPIA for its core data-processing activities already has a significant compliance gap by failing to conduct a PIPIA and may have more. Under the present framework, the risks associated with these compliance failures are not always quantifiable but have, on occasion, proven to be high.
Cross-Border Data Transfer Compliance
For any transaction involving a foreign buyer – or a Chinese target that transfers data to overseas affiliates – cross-border data transfer compliance can be a challenge. Under the Provisions on Promoting and Regulating Cross-Border Data Flows 2024 (2024 CBDT Provisions) and the 2022 Security Assessment Measures, a security assessment is mandatory where: (a) a critical information infrastructure operator (CIIO) transfers important data or personal information abroad; (b) a non-CIIO data processor transfers important data abroad; or (c) a data processor transfers personal information of one million or more individuals abroad or the sensitive personal information of more than 10,000 individuals. As of March 2025, the CAC had concluded 298 outbound data security assessments, 44 of which involved important data; 7 projects were rejected, yielding a rejection rate of approximately 15.9 per cent – indicating a substantive review process, not a rubber-stamp (CAC, Data Outbound Security Management Policy Q&A, 9 April 2025. URL. https://www.cac.gov.cn/2025-04/09/c_1745906286623776.htm; https://www.szzg.gov.cn/2025/xwzx/qwfb/202504/t20250414_5003887.htm).
Cybersecurity and National Security Review
Two separate review mechanisms may be triggered for cybersecurity and national security.
First, the cybersecurity review under the 2025 CSL and the 2021 Cybersecurity Measures is triggered when a CIIO procures network products or services that may affect national security, or where a network platform operator controlling more than one million users applies for an overseas listing (2021 Cybersecurity Measures, Articles 2 and 7).
Second, the foreign investment national security review is administered by the NDRC’s Foreign Investment Safety Review Office under the Foreign Investment Law 2019 and the Measures for the Security Review of Foreign Investment 2020 (effective 18 January 2021). In April 2026, the NDRC used its power to block the Meta-Manus acquisition on data-security grounds following the 2026 NDRC Manus Review, indicating that data and technology assets now have hard national security lines.
Technical Security Measures and MLPS Compliance
Under the 2025 CSL, Article 23 and the 2024 Network Data Regs, Articles 9 and 33, every data processor must implement a set of technical security measures: encryption, access control, security authentication, backup and recovery, and network segregation. These are not optional best practices; they are legal requirements.
The 2025 Shanghai Cases illustrate the consequences of failing to implement such measures. In one case, a logistics IT provider exposed its Elasticsearch database directly to the public, leaving sensitive personal information accessible to unauthorised parties. Regulators found that the company had failed to conduct a cybersecurity-level assessment and had implemented no encryption, access controls or port-security measures. The company was ordered to remediate and fined.
In addition, the MLPS requires every information system to be classified at one of five levels (Level 1 to Level 5) based on the potential harm that would result from a security breach. Systems classified at Level 3 or above must undergo formal security assessments (Note: These are distinct from the data export security assessments).
The Costs of Neglect: Cases and Consequences
The 2026 Manus Review
In what is likely to become the reference case for cross-border AI acquisitions in China, the NDRC’s Foreign Investment Safety Review Office announced its decision in the 2026 Manus Review to prohibit Meta’s acquisition and demanded that the parties withdraw from the acquisition transaction. The deal was reportedly worth over US$2 billion. The NDRC’s final decision affirmed that the deal posed unacceptable risks to data security and national technological sovereignty.
Several aspects of this case are instructive for M&A practitioners:
- First, Manus had relocated its headquarters to Singapore in June 2025, yet the NDRC maintained that the company’s core engineering team and patents remained in mainland China. An offshore holding structure did not shield the deal from review.
- Second, the Chinese Ministry of Commerce had reportedly flagged the deal for potential violations of technology-export regulations under the Export Control Law (2020).
- Third, the two founders of Manus were reportedly restricted from leaving China during the investigation.
In the broader global context, the NDRC’s position could have further-reaching repercussions for other Chinese companies that have relocated their corporate headquarters to Singapore both in China and elsewhere.
The 2025 Shanghai Cases
On 16 January 2026, the Shanghai office of the CAC published the 2025 Shanghai Cases. The cases are notable not for the size of the penalties – most involved warnings and moderate fines – but for the breadth of conduct that regulators found actionable, including:
- Case 1: A logistics technology company exposed an Elasticsearch database to the public;
- Case 2: An IoT services company left system logs containing sensitive personal information exposed to the public internet;
- Case 4: A coffee company was found to have induced user consent through misleading interface design, in violation of 2021 PIPL Article 14; and
- Case 7: A hotel management company failed to comply with cross-border data transfer requirements.
For M&A practitioners, the 2025 Shanghai Cases can serve as a compliance baseline.
Successor Liability
While this article focuses on Chinese law, a US development offers a warning that resonates in the Chinese context.
In April 2025, the US Department of Justice settled a US$8.4 million dispute with a defence contractor and its successor company, Raytheon and Nightwing, resolving allegations of cybersecurity non-compliance that occurred years before the acquisition. The DOJ explicitly named the acquiring company as the successor in liability for the acquired company’s alleged violations.
Under Chinese civil law, the general rule is that a merger or asset acquisition transfers both assets and liabilities – including liabilities arising from regulatory violations under the 2021 DSL and 2021 PIPL. In other words, a buyer will normally inherit liability for past data-compliance violations in addition to any other sums already paid.
Price Reduction for Undisclosed Data Gaps
Data-compliance gaps identified during due diligence can directly affect transaction pricing. For instance, such gaps can justify purchase-price reductions, agreements to share the costs of future litigation and regulatory investigations. Data non-compliance can be used as a negotiating lever – but only before signing.
Allocating Cyber-Risk in Transaction Documents
Representations and Warranties
At a minimum, an acquisition agreement should contain seller’s representations and warranties covering: fair and accurate data mapping; compliance with all applicable data-protection, cybersecurity and privacy laws (including the 2025 CSL, 2021 DSL, 2021 PIPL and the 2024 Network Data Regs); no data breach classified as higher than general in the preceding period, or full disclosure of any such breach, regulator reports, data subject notices and post-mortems; maintenance of a data-classification scheme consistent with 2021 DSL, Article 21; the existence or non-existence of important or core data; the completion of all mandatory PIPIAs under 2021 PIPL, Articles 55 to 56; cybersecurity-level assessments; completion of any required MLPS filings under the MLPS framework and maintenance of all required technical security measures.
For higher-risk transactions – those involving important data, cross-border transfers or AI technologies – enhanced representations should be negotiated, including representations that the target has not been subject to any pending investigation, enforcement action or regulatory inquiry relating to data compliance.
Survival Periods and Caps
General representations and warranties in M&A transactions typically survive for 12 to 24 months after closing. Fundamental representations (such as authority, capital, title to shares, and tax) are recognised in Chinese practice and may survive for significantly longer periods, often three to six years or more, frequently tracking the applicable statutory limitation period. Some M&A contracts may also try to remove caps for fraud and false representations. However, under PRC law the statute of limitations for breach of contract claims is three years from the date the claimant knew or should have known of the breach subject to a maximum limitation period of 20 years (Civil Code, Article 188). Consequently, no unlimited survival period exists as a matter of law.
Conditions Precedent
Where due diligence reveals that a target is engaging in cross-border data transfers without the required approvals under the 2022 Security Assessment Measures or other laws and regulations, the acquisition agreement should make the receipt of approvals from the CAC and relevant industry regulators a condition precedent to closing.
Similarly, where a cybersecurity review is required under 2021 Cybersecurity Measures, Article 7 (e.g., where a network platform operator controlling more than one million users is the target), the buyer should require that the review has been completed or that a clearance letter has been obtained before funds are released.
Indemnities for Breach-Related Losses
The indemnity provisions should expressly cover fines, penalties, third-party claims and remediation costs arising from the seller’s breach of data-compliance representations. Where the target’s data-compliance posture is particularly weak, buyers may negotiate for a specific indemnity escrow or holdback amount to cover potential regulatory fines.
Conclusion
M&A cybersecurity due diligence in China has undergone a fundamental transformation. The days of treating data compliance as a peripheral matter are over.
The combined effect of the 2025 CSL, 2021 DSL, 2021 PIPL and the 2024 Network Data Regs, reinforced by an increasingly complex regulatory framework and stricter enforcement and security review mechanisms, means that data compliance is now central to transaction valuation, risk allocation and feasibility.
For buyers, a thorough due-diligence exercise must integrate three overlapping dimensions: legal compliance (verify that the target satisfies the three laws); technical verification (test whether the target’s security measures are actually deployed and effective, as required by 2025 CSL, Article 23); and, in some cases, national security assessment (evaluate whether the transaction may trigger NDRC review under the Foreign Investment Law or CAC security assessment under the Outbound Data Transfer Measures). A buyer that neglects any of these dimensions will risk inheriting not only a non-compliant business but also the full weight of China’s enforcement apparatus.
For sellers, the stakes can also be high: data-compliance gaps could be discovered and reduce company valuation. Proactive remediation – implementing a proper data-classification scheme under 2021 DSL, Article 21, conducting PIPIAs under 2021 PIPL, Articles 55 to 56, completing MLPS filings under the MLPS framework and documenting technical security measures – is not merely a compliance exercise; it is a value-preservation strategy.